| Prev | Next |
Threat Modeling and Cybersecurity
Any project, development or system can encounter numerous kinds of physical, biological or electronic hazard, which can be identified and scrutinized in a model. You can perform such modeling using the Risk Taxonomy feature. However, as businesses and processes around the world grow increasingly computerized and distributed, the target at biggest risk is the storage and flow of electronic data, the greatest threats are deliberate damage to or infiltration of the data, and the growing business of identifying and mitigating such threats is Cybersecurity.
Enterprise Architect supports the evaluation of Cybersecurity within your organization by providing the Threat Modeling facility, based on the STRIDE Methodology (discussed later in this topic).
Threat modeling overlays process modeling in areas such as UML Activities, BPMN Processes, ArchiMate Processes and Data Flow diagrams. You use the Threat modeling features to encompass areas of the process model and evaluate the threats that might exploit weaknesses in the process. The Threat model depicts the processes, data stores, external entities and their connecting data flows in the business or other system, in order to visually illustrate the potential vulnerabilities of the system. Threat modeling aims at identifying threats that can harm electronic assets, and ensuring that adequate controls to mitigate these threats are covered by security requirements. In essence, Threat modeling is a form of Gap Analysis geared to identifying missing security requirements. The Threat modeling exercise identifies entry and exit points of the system under development that an attacker can exploit. It provides the development team with a perspective of the system from the viewpoint of an attacker or hostile user. It also provides the team with the necessary information to design and test overall project trade-off decisions, by providing insight into the areas that require further investigation from a security aspect.
Threat Modeling:
- Brings a solid foundation for building secure and safe solutions addressing confidentiality, integrity and availability
- Proactively identifies potential security threats and addresses them prior to production
- Identifies vulnerabilities in an existing solution
A Threat model is encapsulated in a Trust diagram, a specific version of a Data Flow diagram. From the diagram, potential threats are identified and, for each threat, mitigations are proposed. In some cases, the mitigation is a change in the design itself, in which case the new or changed elements must be analyzed in an additional iteration. When the mitigations have been implemented, the product or service is validated against the Threat model to ensure that the mitigations work and that design functionality and performance are above standard. If the design has serious security issues, revisiting the design and the Threat model would be appropriate. You can use Threat modeling to shape your application's design, meet your company's security objectives, and reduce risk.
Accessing the Threat Modeling Facilities
Pattern |
Method |
|---|---|
|
Model Pattern |
Select the parent Root Node, View or Package in the Browser window and:
The Model Wizard view displays, showing the 'Threat Modeling Perspective' and the 'Threat Model with Multiple Trust Boundaries' pattern. Click on the Create Model(s) button to load the pattern into the selected Package. |
|
Diagram Template |
Select the parent View, Package or element in the Browser window and either:
The 'New Diagram' dialog displays.
The Diagram View displays ready to populate with objects, and the 'Trust Diagram' page opens in the Diagram Toolbox (see the Trust Diagram Toolbox Page section in this topic). |
|
Diagram Patterns |
When you open a Trust diagram, the 'Trust Diagram Modeling' page opens in the Diagram Toolbox. This is accompanied by a 'Threat Patterns' page, which contains icons to generate a Threat element and Mitigation Checklist element for each of the STRIDE Threat types (see the Security Threats Taxonomy Based on the STRIDE Methodology section, next). Click on the required pattern icon and drag it onto your diagram to generate the elements. |
Security Threats Taxonomy Based on the STRIDE Methodology
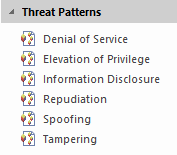
Threat |
Description |
|---|---|
|
Spoofing |
Property: Authentication Spoofing threats involve an adversary creating and exploiting confusion about who is talking to whom. Spoofing threats apply to the entity being fooled, not to the entity being impersonated. So, external elements are subject to a spoofing threat when they are confused about what or whom they are talking to. |
|
Tampering |
Property: Integrity Tampering threats involve an adversary modifying data, usually as it flows across a network, resides in memory, or is stored on disk or in databases. |
|
Repudiation |
Property: Non-repudiation Repudiation threats involve an adversary denying that something happened. |
|
Information Disclosure |
Property: Confidentiality Exposing information to someone not authorized to see it. |
|
Denial of Service |
Property: Availability Deny or degrade service to users. |
|
Elevation of Privilege |
Property: Authorization Gain capabilities without proper authorization. |
Trust Diagram Toolbox Page
You generally pin the Trust Diagram page of the Toolbox in with the Toolbox pages of the process modeling language you are using - UML, BPMN or Archimate.
Note that in order to freely create the relationships in this Toolbox page, you might need to deselect the 'Strict Connector Syntax' checkbox on the 'Links' page of the 'Preferences' dialog.
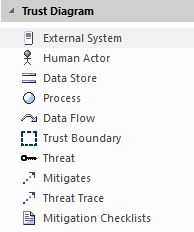
Icon |
Represents |
|---|---|
|
External System |
An external interactor. |
|
Human Actor |
A user. |
|
Data Store |
A generic data store. |
|
Process |
A generic process. |
|
Data Flow |
A directional or unidirectional flow of data between elements. |
|
Trust Boundary |
A border for the boundaries of trust in relation to one or more threats. You use a boundary to enclose a part of the system or process that is either at risk of attack or is secure from attack. The crucial object is the relationship that crosses the borders of both Trust Boundaries. For example, Element A might have an inherent weakness and so is enclosed in a Trust Boundary. Element B is secure and enclosed in a separate Trust Boundary. However, data flows between A and B, crossing the Trust Boundaries and therefore exposing B to a threat from A. |
|
Threat |
A specific type of threat. |
|
Mitigates |
A relationship that assigns a countermeasure, realized by a Mitigation checklist, to a Threat element. |
|
Threat Trace |
A relationship that defines a trace between a Threat element and the threatened elements of a Trust diagram. |
|
Mitigation Checklist |
A Checklist element representing predefined mitigations of a Threat. |
 in the top right corner of the Enterprise Architect screen.
in the top right corner of the Enterprise Architect screen.